November 02, 2010
1

Refer to the exhibit. An administrator documented the output of a CAM table from an Ethernet switch as shown. What action will the switch take when it receives the frame shown at the bottom of the exhibit?
discard the frame
forward the frame out port 2
forward the frame out port 3
forward the frame out all portsforward the frame out all ports except port 3
add station 00-00-3D-1F-11-05 to port 2 in the forwarding table
2
Refer to the exhibit. An administrator issues the commands as shown on SwitchB. What is the result for port Fa0/22?
The port is disabled.
Security is enabled on the port.
The port becomes a trunk port.
The port is now a member of the default VLAN.
3
What is one reason that SSID cloaking is not considered an effective security measure for a wireless network?
The SSID is not required to connect to a wireless network.
The SSID is broadcast in probe messages from clients that are looking for the AP.
The SSID is the same as the AP MAC address, which is sent in every message.
An attacker can spoof the SSID simply by using an SSID of NULL in all messages.
4
Refer to the exhibit. A new host needs to be connected to VLAN 1. Which IP address should be assigned to this new host?
192.168.1.11 /28192.168.1.22 /28
192.168.1.33 /28
192.168.1.44 /28
192.168.1.55 /28
5
While configuring a new switch, a network administrator configures the switch as an HTTP server. What benefits does this configuration provide?
This allows the switch to host web pages for the network.
This allows remote VPN connections to the switch over the Internet.
This is required if a web server or web farm is attached to the switch.This allows web-based configuration tools to be used with the switch.
6
Refer to the exhibit. What will allow a host on VLAN 40 on switch X to communicate with a host in VLAN 40 on switch Y?
QoS
routingtrunking
VPN
7
Refer to the exhibit. A network administrator has designed and implemented a hierarchical network. What is the maximum network diameter between any two hosts on the network?
five
six
ten
twelve
8
A wireless client is attempting to establish a connection with a wireless access point. What process does the client use to discover the access points which are available to it?
probing
beaconing
association
authentication
9
What is the benefit of the auto-MDIX feature on a Cisco Catalyst switch?
dynamically assigns a new management VLAN ID
autonegotiates IP address information for initial management connections
allows the use of straight-through patch cables regardless of connected device types
places a port immediately in the forwarding state to reduce the time for the spanning tree to reconverge
10
Refer to the exhibit. After the listed commands are entered into router R1 and switch S1, the administrator enters the show interface fa0/1 trunk and gets the results shown. What is the likely problem?
The trunk is established, but no VLANs have been configured to use it.
The router is missing the dynamic trunking protocol statements necessary to form a trunk.The trunk has not been established because the router does not support dynamic trunking protocol.
The router, the switch, or both must be configured with the dynamic desirable option for dynamic trunking protocol to establish a trunk.
11
Refer to the exhibit. The hosts connected to switch SW1 are not able to communicate with the hosts in the same VLANs connected to switch SW2. What should be done to fix the problem?
Configure VLANs with different VLAN IDs on switch SW2.Reconfigure the trunk port on switch SW2 with static trunk configuration.
Introduce a Layer 3 device or a switch with Layer 3 capability in the topology.
Apply IP addresses that are in the same subnet to the interfaces used to connect SW1 and SW2.
12
What is the purpose of the switch command switchport access vlan 99?
to enable port security
to make the port operational
to assign the port to a particular VLAN
to designate the VLAN that does not get tagged
to assign the port to the native VLAN (VLAN 99)
13
Refer to the exhibit. Which two statements are true about the operation of the interfaces? (Choose two.)
Incoming traffic with VLAN ID 0 is processed by interface fa0/0.Incoming traffic that has a VLAN ID of 2 is processed by subinterface fa0/0.2.
Both subinterfaces remain up with line protocol up, even if fa0/0 line protocol is down.
Subinterfaces use unique MAC addresses by adding the 802.1Q VLAN ID to the hardware address.
Traffic inbound on this router is processed by different subinterfaces, depending on the VLAN from which the traffic originated.
14
Refer to the exhibit. A network administrator needs to download a previously saved configuration file from the TFTP server to Switch1. Which command will accomplish this task?
Switch1# copy tftp://192.168.0.253/backup-confg nvram:startup-config
Switch1# copy tftp://192.168.0.254/backup-confg nvram:startup-config
Switch1# copy nvram:startup-config tftp://192.168.0.253/backup-config
Switch1# copy nvram:startup-config tftp://192.168.0.254/backup-config
15
What happens when the crypto key zeroize rsa command is entered on a switch configured with the transport input ssh command on the vty lines?
A new RSA key pair is created.
The switch defaults to allowing Telnet connections only.
The switch is no longer able to make SSH connections as an SSH client.
The switch allows remote connections only after a new RSA key pair is generated.
Take Assessment - ESwitching Final Exam - CCNA Exploration: LAN Switching and Wireless (Version 4.0)
www.ccna4u.org
16
Which statement about STP network diameter is correct?
STP diameters are restricted by convergence times.
Layer 2 root elections should be optimized by adjusting BPDU timers to match network diameter.
Using lower bandwidth connections between switches will allow STP to have a larger network diameter.
Portfast can be used to increase the allowable switched network diameter because it disables the forward delay and maximum age timers.
17
In the implementation of PVST+ in a specific VLAN where all switches have default spanning tree priorities, which spanning-tree command setting could be assigned to force one of the Catalyst switches to become and remain the root bridge?
root primary
priority 8192
priority 2048
spanning-tree mode rapid pvst
18
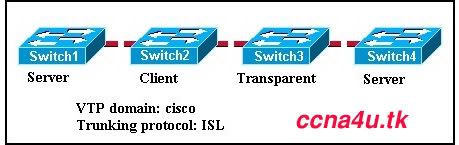
Refer to the exhibit. A new switch, SW3, has been added to the network. The network administrator determines that VLAN information is not propagating to SW3. Which command will remedy the problem?
SW1(config)# vtp version 1
SW2(config)# vtp mode clientSW3(config)# vtp domain Cisco1
SW3(config)# vtp mode transparent
19
In an attempt to improve switch performance, a network administrator changes the MAC aging time to ten seconds. What is a likely result of this decision?
The MAC table will fill with unused addresses.
Address conflicts will cause retransmission errors.
Unnecessary flooding will slow network performance.
Timely MAC address updates will ensure rapid delivery of frames.
20
What is an efficient and cost effective way to minimize the frequency and effects of broadcast storms on an Ethernet LAN?
Connect each PC directly to a router port.
Use access control lists to filter broadcasts from the network.Divide the computers into separate VLANs on the existing switches.
Divide the computers into separate workgroups using different physical switches.
21
Which value determines if a switch becomes the central point of reference in the spanning tree topology?
lowest bridge ID
highest revision number
lowest numeric IP address
highest numeric MAC address
22
Refer to the exhibit. What is the maximum number of VLANs that can be deleted from the Switch as it is configured?
zerofour
five
eight
nine
23
Refer to the exhibit. Switch SW2 was tested in a lab environment and then inserted into a production network without reloading its configuration. After the trunk link between SW1 and SW2 was brought up, all users lost connectivity to the network. What could be the source of the problem?
All the VLANs were pruned from the trunk port between SW1 and SW2.24
SW1 and SW2 cannot be both set as VTP servers in the same VTP domain.VTP configuration revision number of SW2 was higher than the configuration revision number of SW1.
The additional VLANs from SW2 created more VLANs than the VLAN database of SW1 could contain.
Refer to the exhibit. All edge ports are configured with the spanning-tree portfast command. Host1 is recently connected to port Fa0/1 on switch SW1 . Which statement is true about the status of port Fa0/1?
The port will transition into blocking state.The port will transition immediately into forwarding state.
The port will transition into blocking state and then immediately into forwarding state.
The port will transition into blocking state and immediately transition through the listening and learning states.
25
Refer to the exhibit. What does the term DYNAMIC indicate in the output that is shown?
This entry can only be removed from the MAC address table by a network administrator.
When forwarding a frame to the device with address 0060.5c5b.cd23, the switch does not have to perform a lookup to determine the final destination port.
Only the device with MAC address 0060.5c5b.cd23 will be allowed to connect to port Fa0/18.The switch learned this MAC address from the source address in a frame received on Fa0/18.
26
Which type of traffic can still be received on a switch interface that is in STP blocking mode?
BPDU frames
multicast frames
broadcast frames
Layer 3 packets
27
Refer to the exhibit. Hosts B and C attempt to transmit a frame at the same time, but a collision occurs. Which hosts will receive the collision jamming signal?
all hosts that are shown
only hosts B and Conly hosts A, B, and C
only hosts A, B, C, and D
only hosts A, D, E, and F
only hosts D, E, and F
28
Which security protocol or measure would provide the greatest protection for a wireless LAN?
WPA2
cloaking SSIDs
shared WEP keyMAC address filtering
29
Refer to the exhibit. Which statement is true about the status of interface Fa0/1?
The interface is not configured to transmit data.
The interface is configured to transmit data at 10 Mb/s speed.
The interface is configured to transmit data in half-duplex mode.
The interface is configured to use HDLC encapsulation to transmit data.
30
What is the purpose of configuring a switch port as a trunk port?
to control the broadcast domain size
to eliminate the collisions that result from multiple VLANs
to transmit data from multiple VLANs through a single port
to increase the bandwidth between the switch and its upstream device
31
In which mode is a VTP switch operating if it has been configured to only forward VTP advertisements?
client
root
servertransparent
32
When implementing a router-on-a-stick, what must be configured on the router to ensure connectivity between different VLANs?
subinterfaces
routing protocol
switched virtual circuits
dynamic trunking protocol
33
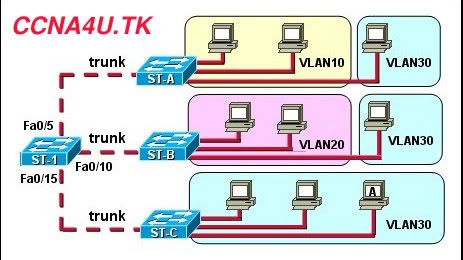
Refer to the exhibit. VTP pruning is enabled in the VTP domain that is shown. How will switch ST-1 handle Layer 2 broadcast traffic originating from host A on switch ST-C?
It will be dropped.
It will be forwarded out port Fa0/5 only.
It will be forwarded out ports Fa0/5 and Fa0/10.
It will be forwarded out ports Fa0/5, Fa0/10, and Fa0/15.
34
Refer to the exhibit. A network administrator needs to add IP phones to the network. To which devices should the IP phones connect?
AS1 and AS2
DS1 and DS2
DS1, DS2, and CS1
AS1, AS2, DS1, and DS2
35
Refer to the exhibit. Each switch is shown with its MAC address. Which switch will be elected as the spanning-tree root bridge if the switches are configured with their default priority values?
switch A
switch B
switch C
switch D
switch Eswitch F
36
Why is MAC address filtering considered a poor choice in securing a WLAN?
Available bandwidth is reduced.MAC addresses are easily spoofed.
APs are more susceptible to DoS attacks.
The payload encryption is easily broken.
37
Refer to the exhibit. What are two reasons for the Fa0/24 port being placed in the blocking state? (Choose two.)
This switch is not the root bridge.The Fa0/24 port is administratively down.STP has detected links that create a loop.
There is a change in the VTP configuration.
The Fa0/24 port is overloaded with too much traffic for its configured bandwidth.
38
Refer to the exhibit. Which two settings show the default value of VTP configuration on a Cisco 2960 switch? (Choose two.)
revision number
existing VLANs
operating mode
domain namepruning mode
39
Company policy requires disabling the command history buffer on network devices. An administrator enters terminal no history size at the command prompt on a Cisco Catalyst switch and receives no error messages back, but the command history buffer is still available. What is the problem?
The command contained a syntax error.
The Cisco IOS version does not support disabling the command history buffer.
The command history can only be disabled on a router, not a switch.The size parameter reset the default buffer size but did not disable access to the buffer.
40
Refer to the exhibit. Which Spanning Tree Protocol version is in effect?
Per VLAN Spanning Tree (PVST)
Per VLAN Spanning Tree + (PVST+)
Common Spanning Tree (CST)Rapid Spanning Tree Protocol (RSTP)
Multiple Spanning Tree Protocol (MSTP)
41
Refer to the exhibit. All switch interfaces are members of the same VLAN. What information is used by Switch1 to determine if incoming frames from the hosts should be forwarded to Router1?
the source address field in the IP header
the destination port number in the TCP header
the destination address field in the Layer 3 header
the destination address field in the Ethernet header
42
Refer to the exhibit. The configuration steps that are listed in the exhibit have been entered in switch S1 via the console. Subsequent attempts to telnet to the switch are not successful. What is causing the problem?
The switch must be configured with SSH version 1.The transport input command must specify Telnet access.
The RSA keys must be returned to zero before SSH will permit Telnet access.
The ip domain-name command must also be entered in line configuration mode for the vty lines.
43
What provides an authentication mechanism for 802.11-based wireless networks?
DSSS
OFDM
SSIDWPA
44
How does a switch that is configured for 802.1Q trunking handle untagged frames that are received on a trunk port?
The frames are dropped.
The frames are assigned to the native VLAN.
The frames are assigned to the default VLAN.
The frames are assigned to the management VLAN.
45
Why is it advisable that a network administrator use SSH instead of Telnet when managing switches?
SSH uses TCP whereas Telnet does not.
SSH encrypts only the username and password when logging in.SSH encrypts all remote management communications whereas Telnet does not.
SSH sends a clear text message steam which reduces the bandwidth use for management.
46
What are two requirements for configuring inter-VLAN routing using the router-on-a-stick model? (Choose two.)
Each subinterface should be configured with its own IP address, subnet mask, and unique VLAN assignment.The physical interface of the router must be connected to a trunk link on the adjacent switch.
The number of physical interfaces on the router should match the number of VLANs.
Different static VLANs should be assigned to different interfaces of the router.
The router should be configured as the VTP server.
47
Refer to the exhibit. Users A and B are reporting intermittent connectivity problems. Pre-installation surveys showed strong signal strength from the AP locations to the client locations. Outside electrical interference has been eliminated. What will fix the problem?
Relocate the APs closer to each other.
Increase the distance between the clients.Change the channel on AP-B to 6 or 11.
Place AP-A and AP-B on the same wireless channel.
48
What is a function or characteristic of the native VLAN?
It is the VLAN that supports untagged traffic on an 802.1Q trunk.
It is always assigned to VLAN 1 for backward compatibility.
It is always the same VLAN number for all trunks within an organization.
It is used as the management VLAN throughout the entire switched network.
49
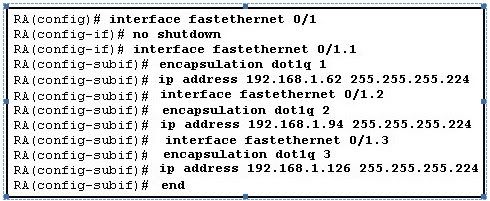
Refer to the exhibit. Which three options correctly describe the router configuration that is shown? (Choose three.)
An IEEE standard trunking protocol is in use.Interface Fa0/1 has been configured with subinterfaces.
The shutdown command has been applied to interface Fa0/1.
Interface Fa0/1.3 is mapped to the default management VLAN.The configuration is appropriate for a router-on-a-stick network design.
An IP address should be applied to interface Fa0/1 for routing to occur.
50
Refer to the exhibit. All hosts are in listen mode. Host 1 and Host 4 both transmit data at the same time. How do the hosts respond on the network? (Choose two.)
After the end of the jam signal, a backoff algorithm is invoked.
Hosts 1 and 4 are operating full duplex so no collision will exist.
The hub will block the port connected to Host 4 to prevent a collision.
Hosts 1 and 4 are assigned shorter backoff values to provide them priority to access the media.If a host has data to transmit after the backoff period of that host, the host checks to determine if the line is idle before transmitting.
51
What is the purpose of VTP pruning?
to restrict traffic on specified trunk lines
to designate switches that do not participate in VTP
to advertise VTP domain information to specified switches only
to reduce the propagation of VTP advertisements in the switched network
52
What operational change will occur if an 802.11b client associates with an access point that is currently supporting clients utilizing 802.11g?
The 802.11g clients will disassociate from the AP.
The 802.11g clients will operate at reduced speeds.
The 802.11b client will never gain access to the channel.
The 802.11b client will not be able to establish an IP session with any of the other 802.11g clients.